Security of Advanced Access Content System
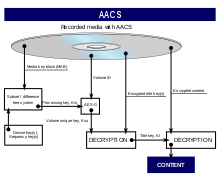
The AACS system relies on a subset difference tree combined with a certificate revocation mechanism to ensure the security of high definition video content in the event of a compromise.
[1] Concerns about the approach included its similarity to past systems that failed, such as CSS, and the inability to preserve security against attacks that compromise large numbers of players.
Jon Lech Johansen, who was part of the team that circumvented CSS, said he expected AACS to be cracked by the end of 2006 or the beginning of 2007.
[4][5] While great care had been taken with AACS to ensure that content was encrypted along the entire path from the disc to the display device, it was discovered in July 2006 that a perfect copy of any still frame from a film could be captured from certain Blu-ray and HD DVD software players by using the Print Screen function of the Windows operating system.
Such approaches do not constitute compromises of the AACS encryption itself, relying instead on an officially licensed software player to perform the decryption.
[15] Some administrators of sites which consist of user-submitted content, such as Digg and Wikipedia, tried to remove mentions of the key fearing reprisals from AACS LA.
[20] [21] To continue having the ability to view new content users were forced to apply the patches, which also hardened the security of player applications.